
Even before the 2020 pandemic, it was becoming clear work is no longer a location, it is an activity. Previously, work used to be a location we all went to – as in “I have to go to work” – but now employees no longer need to go “someplace” to perform duties, rather they can just work from anywhere.
Besides the changes driven by the pandemic (now mostly behind us), two major underlying factors contributed to this change:
- Apps are now everywhere – organizations are shifting to a model where you no longer consume apps strictly at the data center. The app delivery model – with SaaS, with cloud, etc. – is now hybrid. The majority of organizations utilize some combination of private cloud, public cloud, Internet, and SaaS – which is rapidly becoming the default app delivery model.
- Users are now everywhere – organizations today have also adopted a hybrid work model, supporting either partially remote (working out of a home office two to three days a week), completely remote, or anything in between. While this new work model affords a great deal of flexibility, there is no tie-in anymore to the traditional model of work being a place.
These factors mean that the attack surface now expands exponentially. The new reality inverted access requirements, with more users, devices, applications, services and data located outside of an enterprise than inside.

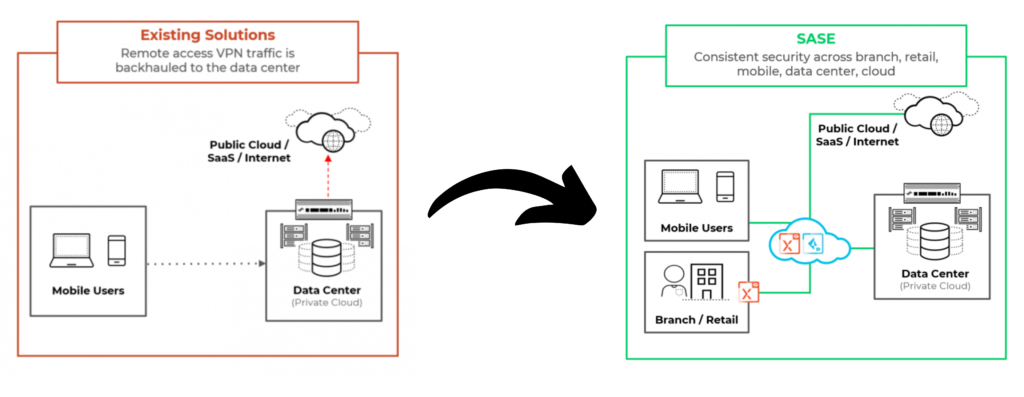
The VPN approach does not work anymore
The typical legacy VPN approach simply does not work anymore, as more and more applications and access locations “escape” security inspection.
It turns out that moving both remote access infrastructure and security inspection to a service layer in the cloud can solve both the modern security challenges and also reduce the infrastructure costs.
In 2019, Gartner published research that described how security and remote access technologies would begin to converge into what’s known as a Secure Access Service Edge (or SASE, pronounced “sassy”).
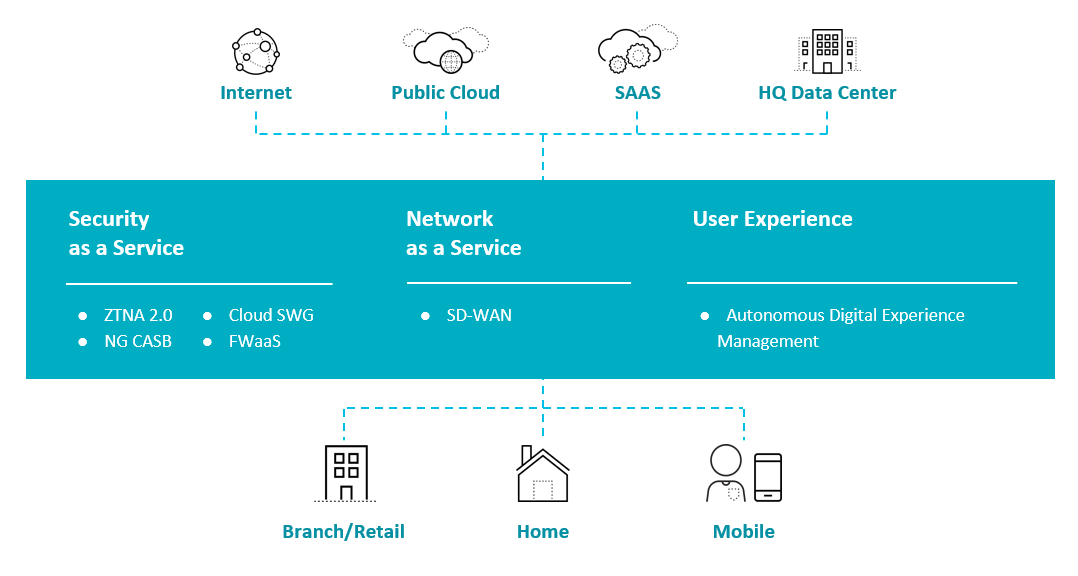
With SASE, organizations can easily:
- apply the principles of least privilege access and continuous trust verification based on client behaviors and device posture changes – this is known as Zero Trust Network Access (ZTNA)
- deliver continuous security inspection for all traffic to protect against all threats and threat vectors (Application and URL filtering, DLP, anti-malware, etc.)
- Protect and secure all applications across the entire enterprise, and regardless of employee location.
Want to learn more? Apply for our practical workshop on SASE.

